Unrestricted Warfare = No Boundaries
When an adversary tells you what they plan to do, you should probably listen...
Prescott, AZ March 30, 2024… What do boats, bridges, and code have to do with elections? The book, Unrestricted Warfare: China's Master Plan to Destroy America, written by two Peoples Liberation Army (PLA) colonels, is a collection of documents that admittedly, “carefully explores strategies that militarily and politically disadvantaged nations might take in order to successfully attack a geopolitical super-power like the United States.
American military doctrine is typically led by technology; a new class of weapon or vehicle is developed, which allows or encourages an adjustment in strategy. Military strategists Qiao Liang and Wang Xiangsui argue that this dynamic is a crucial weakness in the American military, and that this blind spot with regard to alternative forms warfare could be effectively exploited by enemies. Unrestricted Warfare concerns the many ways in which this might occur…”
The lifeblood of America is code…
From the employment of JITS (just-in-time shipping) to stock store shelves with groceries and perishable goods, and law enforcement, fire, and emergency medical service response to calls for service, to elections and national defense, everything runs on machine code, aka software. And in the 5G world known as the “Internet of things” it is all vulnerable to cyber-attacks. It is indeed the cyber-border where many intrusions go undetected, and it is perhaps the most significant exposure to disruption, maybe even full-scale destruction to the American way of life.
SEP 17, 2014 WASHINGTON – Hackers associated with the Chinese government successfully penetrated the computer systems of U.S. Transportation Command contractors at least 20 times in a single year, intrusions that show vulnerabilities in the military’s system to deploy troops and equipment in a crisis, a Senate Armed Services Committee investigation has found.1
America's computers are under attack and every American is at risk. The United States Government, critical infrastructures, American business institutions, and our personal data are being compromised by nation-states and hacker groups. Chief among those actors is the Chinese Communist Party (CCP) apparatus, the very same set of actors that Joe Biden regularly claims is not a threat but can serve American interests. That is about as naive as using a full-grown alligator for babysitting a two-year-old.
The radical-left Brookings Institute says, “According to Secretary of State Antony Blinken, the new administration's approach to China will be “competitive when it should be, collaborative when it can be, and adversarial when it must be.” The Biden administration has reaffirmed the desire for collaboration and cooperation with China in areas that serve American interests.”2
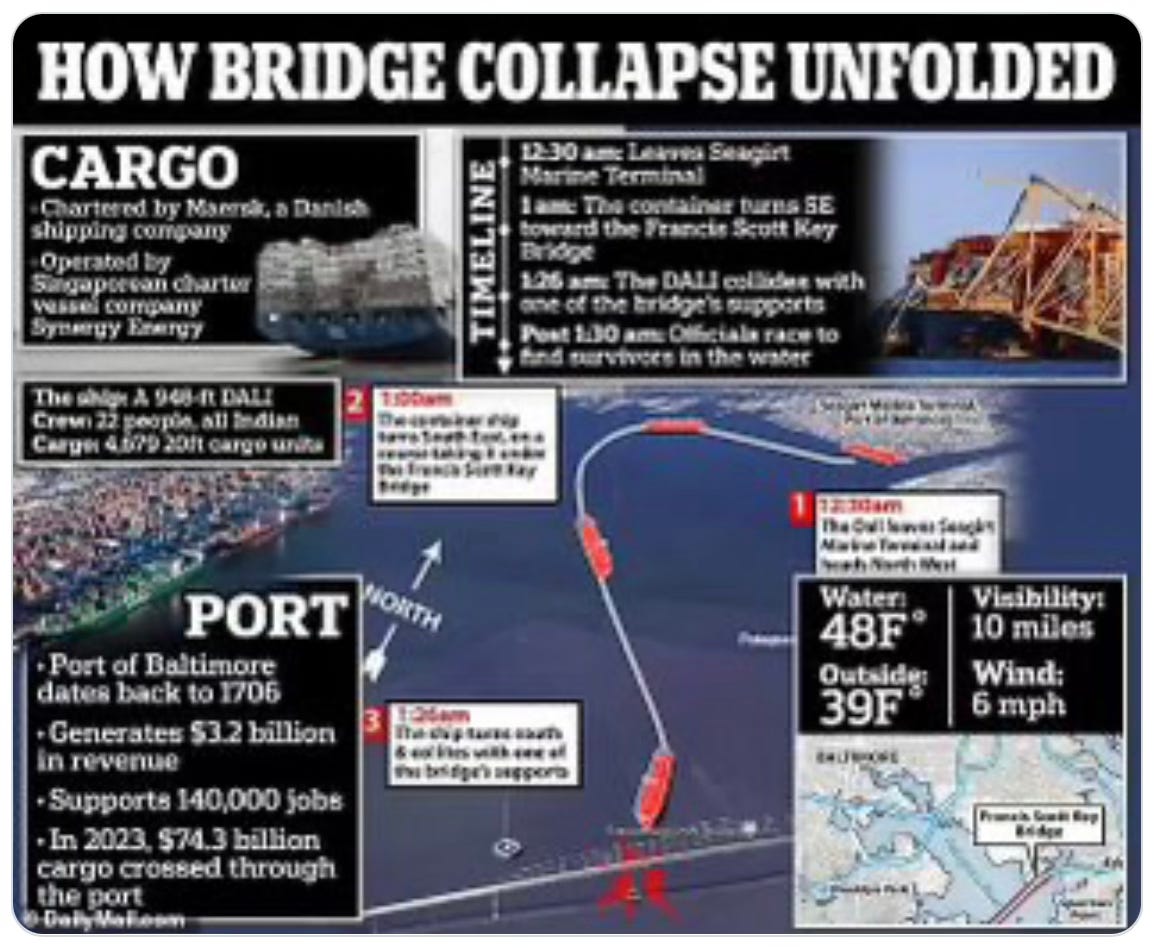
Critical thinkers are not buying the narrative that the recent collision involving the ship Dali and the Francis Scott Key Bridge was an accident. There are too many abnormalities about this event that just don’t add up. Initially the claim was that the ship lost power a few times as it moved down the waterway, and in so doing, lost the power to move the rudder, yet the ship made a hard move to the starboard (right) at precisely the right time to line up a strike at a supporting pylon for the bridge.
Why is CISA providing commentary on the incident?
CISA (the U.S. Cybersecurity and Infrastructure Security Agency) is providing commentary on the Baltimore Harbor incident. Isn’t NTSB (the U.S. National Transportation Safety Board) the authoritative agency in command?
While the NTSB is just opening its investigation, CISA already says, “the ship lost propulsion as it left port,” yet it still took an hour to get to the bridge. During the movement through the harbor, the ship makes a wide sweeping turn to port (left), and then, just before it slams into a main support pylon, it makes a hard starboard movement, dropping the span into the water, essentially closing the harbor to all shipping, maritime, and military. The video of the ship's movement is widely available for viewing.
If it lost power, then how did it turn for an hour?
Wasn’t the initial claim that it lost power just minutes before impact?
If entry into the channel is a critical safety concern, where are the tug boats?
If the ship was powerless and uncontrollable, why were the anchors not dropped?
If the ship is controlled by code, was an anchor drop prevented?
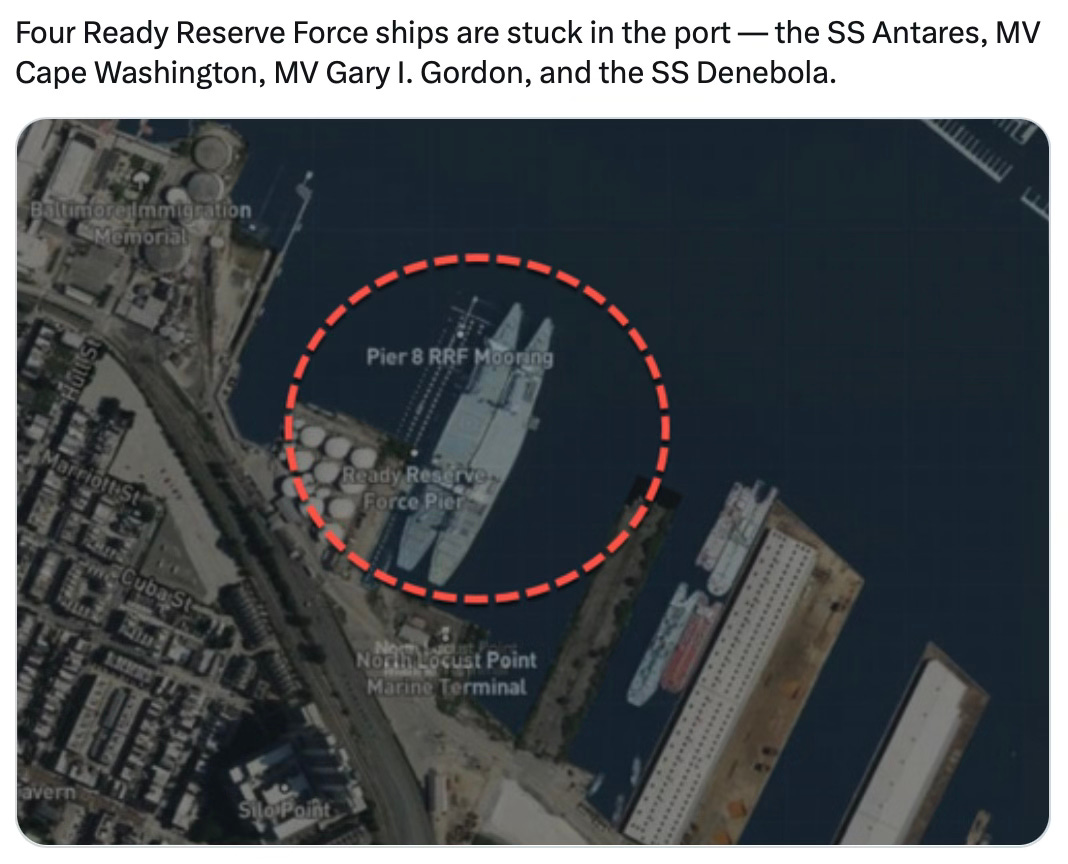
CISA’s entry into the narrative stream reveals that there is a serious potential for the nefarious seizure of the ship’s controls, using code. This is a relatively low-tech means to not only cripple a major route for the movement of goods along the eastern seaboard but also creates a serious challenge to the U.S. Navy.
This domestic event calls into question all cybersecurity…
The mountain of theories will be winnowed down to those with the greatest evidence. Of all federal agencies, the one most trustworthy is the NTSB, it seems the least corruptible because it relies on evidence and real science. On a scale of suspicion, how likely is it that a cyber-intrusion took control of the ship? It must be ruled out, especially since the ship’s navigation system relies on satellite management. Click the link for real-time ship movements to see just how reliant the maritime industry is on cyber-communication.
When the unexpected occurs, whether in shipping collisions or elections, we must rule out a cybersecurity breach. The potential threat to election systems should be obvious to every policymaker and elections official in America. Blind allegiance to a potentially compromised system, especially when evidence is produced of such a vulnerability is maladministration.
Past behavior is a key predictor of future performance.3 The trustworthiness of CISA and Krebs himself has been in question since November 12th, 2020, just 9 days after the General Election when swing states stopped counting votes simultaneously. 100% of those vote-counting systems are in the cybersecurity sphere of influence. And not one county did a full ballot count comparison with electronic “tabulation.” Instead, tens of millions of dollars have been spent on litigation to prevent code inspection and ballot count comparisons, and those who advocate for them have been vilified and tried for rocking the boat by the election machine cult.
Keep reading with a 7-day free trial
Subscribe to Mark Finchem's Inside Track Substack to keep reading this post and get 7 days of free access to the full post archives.